The Center for Education and Research in Information Assurance and Security (CERIAS)
The Center for Education and Research inInformation Assurance and Security (CERIAS)
Want to get some authentic CERIAS and Spaf swag? Read on!
CERIAS offices are moving in a matter of weeks. We don't want to have to box up everything, especially items we aren't likely to use any time soon (if ever) at the new location. Plus, some of these things are items we've heard people might like to have for themselves.
So.... We're going to give some of it away!
What's the catch? Well, we want to encourage people to do something good for others. And, as an institute (CERIAS) at a university (Purdue) and a life-long educator (Spaf), we thought that helping deserving students get cybersecurity education would be the way to do that.
To get some of the swag, as listed below, you need to make a donation to one of these charitable scholarships no later than August 5th, and provide proof of the donation and amount. We'll then package up your gifts and send them (we'll cover shipping inside the United States; if you are outside the U.S. we'll need to negotiate the shipping and any customs).
What charities? Only some of the best for cybersecurity students, and all established in memory of some pioneers in the field:
We'll note here that these are also worthwhile for regular donations. As non-profits, there may be tax advantages to your donations. And be sure to check if your employer has a matching donation program!
We have established the donation. What's the swag? While supplies last:



First, make a qualifying donation to one of the charities. Send proof of the donation, your address, and your shirt/hoodie/jacket size to: <spaf@cerias.purdue.edu>. You'll get the listed items while supplies last. If we run out of an item we will substitute an item of equal or better value.
| Minimum donation | Items shipped |
|---|---|
| $150 | 2 of Spaf's coffee mugs plus a CERIAS challenge coin |
| $200 | An additional item of CERIAS-branded merchandise plus 1 CERIAS mug |
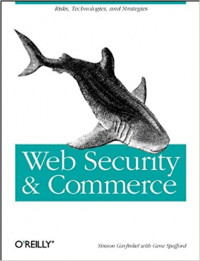
| $300 | A copy of the book in addition to the above, plus an additional CERIAS item. | $500 | All of the above, plus 2 additional coffee mugs, plus a CERIAS logo fabric briefcase or portfolio. |
Remember, these are really all extra gifts. The real value is you making a donation to a worthwhile charity to help some deserving people study cybersecurity!
While cleaning out the storage closet we found a dozen remaining Spaf bobbleheads. This is the last of this collector's item! 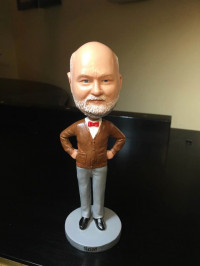 To get one, send us a check for a minimum of $100 made out to "Purdue University" with "Donation to CERIAS" on the memo line. (And, to be clear, Purdue University is also a non-profit entity.) Send the check with your return address to:
To get one, send us a check for a minimum of $100 made out to "Purdue University" with "Donation to CERIAS" on the memo line. (And, to be clear, Purdue University is also a non-profit entity.) Send the check with your return address to:
Bobblehead c/o Shawn Huddy
CERIAS -- Purdue University
656 Oval Drive
West Lafayette, IN 47907-2086
In May of 1998, Purdue chartered CERIAS -- the Center of Education and Research In Information Assurance and Security -- as a campus-wide, multidisciplinary center for the new (at the time) field of cybersecurity. CERIAS grew out of the COAST Laboratory in the CS department. Our original core of a half-dozen faculty spanned several of the departments and colleges at Purdue and thus warranted a university-level institute.

As part of its commitment to the new center, Purdue University renovated most of the 2nd floor of the Recitation Building on the central campus for CERIAS. The 2nd floor was originally classrooms. We moved into the redone space in early 1999. The space involved a conference room, a small library, a small kitchen and lounge, offices for 10 faculty and staff, and a half-dozen shared offices for grad students. We also had two dedicated rooms on the 4th floor -- one as a protected machine room, and one as a lab.
The space in REC has served us well since then. We were located near the CS, ECE, and CNIT departments, in a building with great character, including flooring made from birds-eye maple planks. We also had to cope with some of the idiosyncrasies of an older building, including cranky HVAC and leaky pipes. (Recitation was originally completed in 1923.) CERIAS grew into a world-renowned entity with over 150 associated faculty across campus and many hundreds of their students.

Over the last few years in particular, Purdue overall has prospered, with increasing prestige and growing enrollment. Last year, Purdue had over 50,000 students enrolled at the main campus! Having frozen tuition for a decade has undoubtedly helped to make a Purdue education even more attractive, despite the increasingly-rigorous admission standards. There has been an associated boom in new buildings -- with over two dozen new dormitories, laboratories, and co-working space for collaborations with companies and national labs. This has included construction of the Discovery Park District.
Last year, as part of a master planning process, university administration decreed some reorganization. Many administrative and academic programs are moving to accomodate growth, move related groups near each other, and make better use of space. That includes CERIAS!
As of August 15, we are bidding adieu to Recitation. For the following 4 months we will be virtual as our new "galactic headquarters" is being finished. Meanwhile, our space in Recitation will be renovated info offices and meeting space for the Dean of Students
In January, we will be moving into our new offices and lab space on the 3rd floor of the Convergence Center on campus. Convergence is part of the public-private partnerships idea that Purdue has been promoting over the last few years. It is a building owned and operated by a private company, located on the university and housing several campus departments as well as industry offices. It was completed in 2020 and presents exciting new possibilities for our next 25 years.
Our new space will be bright and airy, with lots of windows. We'll have more offices, lots of work spaces for students, several labs, and multiple meeting rooms. We'll also have dedicated space for co-location of researchers of some CERIAS partners (with Sandia National Labs the first such partner).
If you want to visit us between August 15 and January 15, let us know and we'll find a room on campus to meet with you. After the 15th, come visit us at our new offices!
Our new address will be:
During and after the transition we expect our phone numbers and email addresses to be unchanged. Our web pages will continue to be active. Our phones will forward to wherever we are during the build-out phase, so you will be able to reach us as always.
While we're at it, mark your calendars for March 28 & 29 --- the annual CERIAS Symposium. We're celebrating our 25th anniversary and you are all invited!
Last week was our 23rd CERIAS Symposium. It was a great event, thanks to great speakers and lots of behind-the-scenes work by the wonderful staff. We have developed a history of some outstanding presentations and interactions. Next year we will be celebrating the 25th anniversary of the founding of CERIAS (it will be the 24th symposium because we didn't have one the first year). I hope we can continue the streak of great presentations and events, but given the tremendous community we have, I'm sure that will be the case.
During the breaks, I ran into several former students, including one who graduated 28 years ago. I heard wonderful stories about what they've been doing in their lives since then, and how their experience at Purdue with COAST and CERIAS helped set them up for success. That is really gratifying to hear; teachers always like some affirmation that they didn't screw up too badly!
I was going to write up a blog post here about that -- no doubt prompted by my last post about the workshop 22 years ago -- then I vaguely recalled having written something like that a while back. After some looking, I found it in my personal blog (it was before we established this blog): Some Thoughts on Lifetime Achievement. That has mostly aged well, and I could make most of the same general comments today. I continue to be pleased that my former students are happy and productive. And although I am still sure I will be forgotten in 100 years (heck, a lot of people try mightily to forget me today), I am confident that what I helped start as education and awareness in this space will continue to make a difference through the good works of those whose lives we touched here at Purdue.
Also, I'm still not done yet. I have 5 Ph.D. students in various phases of completion plus two books underway with ideas for more, and I hope to get all those things finished before I think seriously about voluntary retirement. However, given the state of reality and current events, voluntary may not be the only route....
I may have to spend more time looking through things I wrote over the last 30 years to see how/if some of my thinking has evolved. This makes two items from the archives I had dimly remembered that seem to be relevant now. But I will note that in 11 years I have never found a use for my AARP card that my AAA membership didn't also provide (e.g., hotel discounts).
While preparing to introduce today’s keynote (Dr. David McGrew) at the 23rd CERIAS Symposium, I was reminded of an exercise in crystal ball gazing. Every December we have various people publish a list of their top predictions for the coming year. Some are thoughtful, and others simply risable. The track record is often quickly forgotten.
However, what of an effort by real experts and visionaries to make some bold predictions for a decade hence? Many people have repeatedly claimed that such a thing is impossible for cybersecurity – the field moves too quickly, innovation disrupts truisms, and biases complicate the mix.
Here, I present at least one worked example that proves that it could be done – and was.
In 1992, the COAST Laboratory was started. Around 1996, Cisco became a corporate partner with COAST, providing equipment and funds for student scholarships. When CERIAS emerged from COAST in May 1998, Cisco stepped up as a founding sponsor. This included not only continuing financial support, but increasing some researcher involvement.
In 2000, another CERIAS partner at the time, Accenture, agreed to cosponsor a workshop at their St. Charles conference center. The workshop would be organized by CERIAS and was to focus on making some “bold” predictions for the next decade. We were supposed to identify some “visionaries” who could participate and discuss the future.
I (Spaf) identified some personnel I knew were deep thinkers, some of whom were not yet quite widely known in cybersecurity. I invited them, and Accenture added a few of their own senior staff. These people went on to build significant reputations in the field. (I’d like to claim it was because they participated in the workshop.)
The visionaries who attended, and their affiliations at the time:
An impressive group, in hindsight; fairly impressive in 2000, too!
I won’t recapitulate the whole workshop report, which you can read if you wish. However, I will summarize what we saw as the top 10 trends for cybersecurity in 2000:
I remember when the report came out it was dismissed by some in industry as “too pesimistic.” Perhaps because the “visionaries” weren’t all well known, the conclusions were largely ignored.
Looking back on the list, I’d say we scored at least 90%, especially for the decade that followed. Both #3, and #10 took a little longer to manifest, but we were on target with all ten.
You can apply some hindsight bias now to say they were all obvious, but that really wasn’t the case in fall 2000. The iPhone was 6 years away from introduction and the Motorola StarTac CDMA phone was effectively the state-of-the-art. Wireless was basically defined by the recent release of 802.11a/b. Internet penetration was less than 6% of the world’s population (it is over 66% now, in early 2022). At the time of the workshop, Facebook and Twitter were years away from creation, and Google was a small search engine company less than 3 years old. Ransomware had been described theoretically, but would not become prominent for several years.
Interestingly, the action items the group defined are still relevant, and notable perhaps in how they are still not practiced widely enough:

One of the workshop participants informs me that the workshop was held in late September 2000. The report is copyrighted 2001, which is why I thought that is when it was held that year. Unfortunately, I no longer have my appointments calendar from that time so my initial posting indicated 2001. His recollection of this is strong, and is likely correct. I have corrected the dates in the entry above to reflect this correction.
In 1975, the illustrious Dorothy Denning received her Ph.D. from Purdue’s CS Department. Thereafter, she became an assistant professor, and then associate professor in 1981. Her most notable advisee was Matt Bishop, who graduated with his Ph.D. in 1984.
Dorothy initiated a graduate class in cryptography, CS 555, using her book Cryptography and Data Security, around 1980. That class is still taught today (with regular updates), perhaps making it the longest-running cybersecurity class in academia.
In 1983, Sam Wagstaff, Jr. (now a professor emeritus) joined the Purdue CS faculty as an expert in cryptography and algorithms. In 1988, Eugene Spafford joined the Purdue CS faculty with expertise in software engineering and distributed systems; Spaf also had a long-standing interest in information security, but not as an academic concentration. (Both Sam and Spaf have taught CS 555 over the years.)
Most of the academic research around the world in the 1970s and 1980s into what later became known as “cybersecurity” was focused on formal methods, authentication models, and cryptography. Some security research was secondary to OS security, database, and architecture, but it was not a particularly distinct topic area in classes or academic research. There were only 2 or 3 universities with any identifiable expertise in the overall topic area, outside of cryptography and formal methods of software development.
The Cuckoo’s Egg incident in 1986, and the Internet Worm in 1988 helped generate a great deal of interest in more applied security. Spaf had involvement in both, and especially notable in the Worm incident. Subsequent growth of instances of hacking and malware brought increased interest including some funding for research.
Early Purdue successes included release of COPS (developed by Dan Farmer under Spaf’s direction), and the publication of Practical Unix Security, co-authored by Spaf and Simson Garfinkel. Both brought attention to Purdue.
Increased student interest in computing security coursework and external funding from companies and government agencies led to Spaf and Sam establishing the COAST Laboratory within the CS department in the fall semester of 1991. The CS department provided a room for the lab and student office spaces. Four companies made generous donations to equip the lab initially: Sun Microsystems, Bell Northern Research, Schlumberger, and Hughes Laboratories.
The name COAST was suggested by Steve Chapin, one of Spaf’s Ph.D. students. It is an acronym for “Computer Operations, Audit, and Security Tools,” reflecting the more applied focus of the group. Steve was the first Ph.D. graduate from the lab, in 1993.
In the next few years, COAST became notable for a number of innovative and groundbreaking projects, including the Tripwire tool, the IDIOT intrusion detection system by Kumar, vulnerability classification work by Aslam and Krsul, the first-ever papers describing software forensics by (individually and as a group) Krsul, Spafford, and Weeber, discovery of the lurking Kerberos 4 encryption flaw by Dole and Lodin, the firewall reference model by Schuba, and the first online (ftp, gopher, and www) repository of cybersecurity tools; a remnant of that repository with many historical artifacts is available online. Many other people also contributed to notable successes, some of whom are noted below.
In 1992, COAST began to host a regular seminar series of local and invited speakers. That seminar series continues to this day; there is an archive of talk descriptions (from 1994 onwards) and videos (from late 1999 onwards). The series has featured a veritable “Who’s Who” of people in cybersecurity research, industry, and government. The series continues to attract viewers worldwide, and the entire collection is available for free viewing.
Despite the growing interest, in 1997, when Spaf testified before the House Science Committee, there were only three identified academic centers other than at Purdue. Shortly thereafter, continued growth and faculty involvement led to the transformation of COAST into the campus-wide institute CERIAS, in May of 1998. That will be the topic of a later post.
As of now, however, congrats to all the people who contributed to the founding and growth of COAST – celebrating its 30th anniversary this academic year!
A number of students completed their degrees and worked in COAST, most under the direction of Professor Spafford. Here are a few of them: